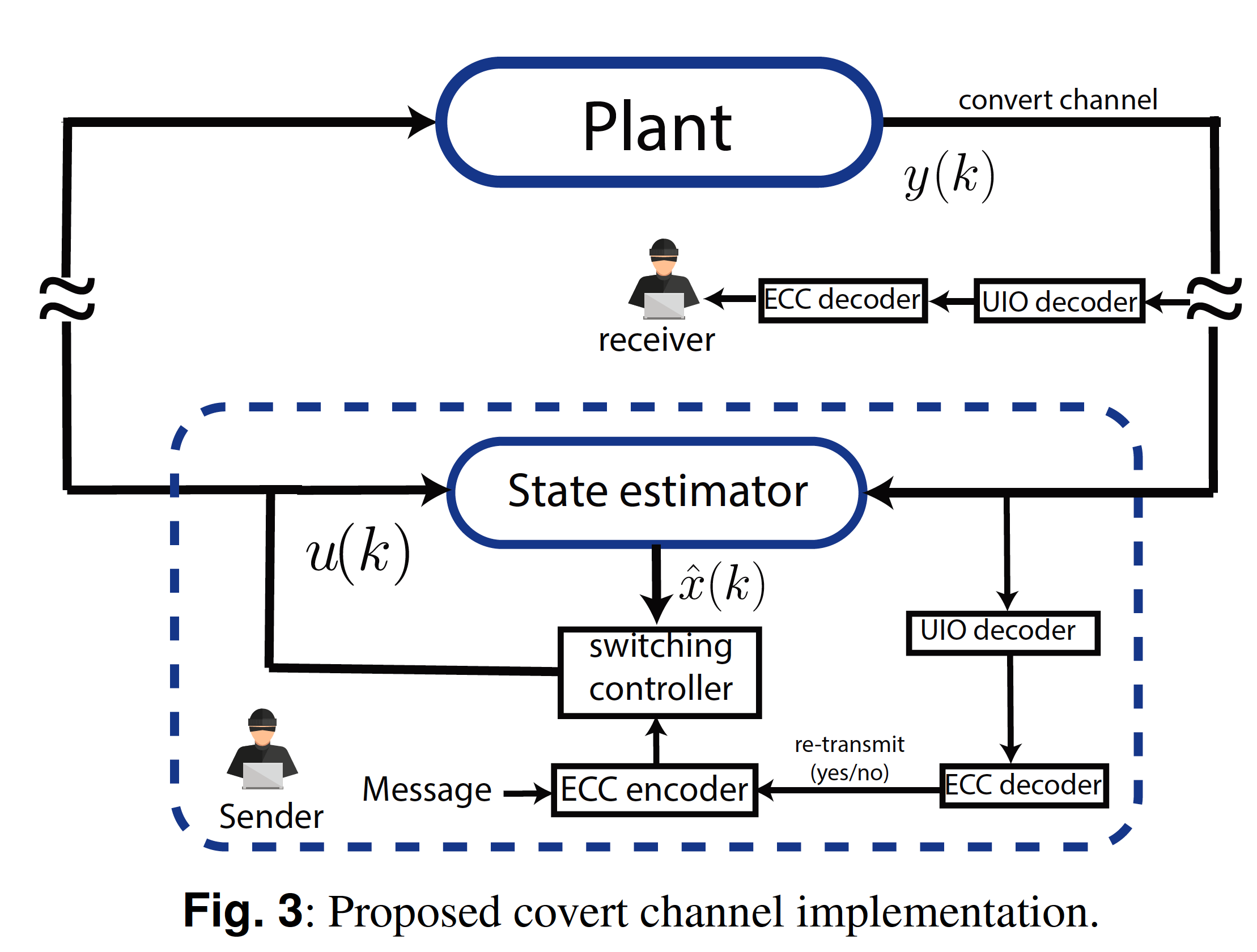
A covert channel is a communication channel that is not intended to exist, and that can be used to transfer information in a manner that violates the system security policy. Attackers can abuse such channel to exfiltrate sensitive information from cyber-physical systems (CPSs), e.g., to leak the confidential or proprietary parameters in a control system. Furthermore, attacks against CPSs can exploit the leaked information about the implementation of the control system, e.g., to determine optimal false data injection attack values that degrade the system performance while remaining undetected. In this paper, we present a control theoretic approach for establishing covert channels in stochastic CPSs. In particular, we consider a scenario where an attacker is able to inject malware into the networked controller and arbitrarily alter the control logic. By exploiting such capability, an attacker can establish an illegitimate communication channel, e.g., to transmit sensitive plant parameters, between the networked controller and an eavesdropper intercepting the sensor measurements. We show that such a channel can be established by exploiting the closed-loop system operations, a decoding mechanism based on an unknown input observer, and an error-correcting coding scheme that exploits the control loop to obtain an implicit acknowledgement. A simple proof of concept implementation of the covert channel is presented, and its performance is evaluated by resorting to a numerical example. Finally, we propose some defences and countermeasures against the proposed covert channel.
W. Lucia and A. Youssef, "Covert Channels in Stochastic Cyber-Physical Systems," IET Cyber-Physical Systems: Theory & Applications, DOI: 10.1049/cps2.12020, 2021.